China’s Wing Loong 2 Is Spoofing Transponder Signals Over the South China Sea in What Analysts Call a Taiwan Rehearsal

Check out the Best Deals on Amazon for DJI Drones today!
A Chinese military drone has been flying regular surveillance missions over the South China Sea since August while broadcasting false transponder codes that made it appear to be other aircraft entirely — including a sanctioned Belarusian cargo plane and a Royal Air Force Typhoon fighter jet. At least 23 flights have now been logged. Analysts who track People’s Liberation Army air operations say the pattern is not accidental, not experimental, and not subtle. They call it a live deception trial.
- The Development: A Wing Loong 2 drone flying under call sign YILO4200 has transmitted false ADS-B registration codes on at least 23 flights from Hainan’s Qionghai Boao Airport, according to a Reuters investigation analyzing data from Flightradar24.
- The “So What?”: Flight paths from the Hainan operations, when overlaid on a map of Taiwan by analysts, pass directly over multiple military points of interest concentrated around Taipei — a pattern Singapore-based analyst Alexander Neill describes as “rehearsals for a confrontation,” not routine exercises.
- The Spoofed Identities: The drone has impersonated a Rada Airlines Ilyushin-62 (a Belarusian carrier on the US Treasury’s OFAC sanctions list), an RAF Typhoon, a North Korean passenger jet, and an anonymous Gulfstream executive aircraft.
- The Verdict: Ben Lewis, founder of open-source tracking platform PLATracker, told Reuters: “We have not seen anything like this before. It does not appear to be at all accidental.”
The Wing Loong 2’s Deception Campaign in the South China Sea
The Wing Loong 2, produced by the state-owned Chengdu Aircraft Industry Group (CAIG) — a subsidiary of AVIC — is a long-endurance unmanned aerial vehicle with a 20.5-meter wingspan broadly comparable to the US MQ-9 Reaper. It is primarily a surveillance platform but can be configured for command and control, precision missile strikes, or anti-submarine warfare. The aircraft flying call sign YILO4200 has been operating out of Boao Airport, a dual-use commercial and military facility, where satellite images from July, September, and January show large drones on the tarmac alongside recently expanded support infrastructure.
The spoofing works through ADS-B transponders. Aircraft registration numbers are encoded as unique 24-bit addresses governed by the International Civil Aviation Organization (ICAO) and broadcast publicly to reveal position, speed, and heading. Two pilots and two analysts who spoke to Reuters confirmed that recoding a transponder to broadcast a different aircraft’s address is technically possible. Flightradar24 communications director Ian Petchenik said his platform had noticed the Hainan flights and had never seen anything like them beyond apparently accidental miscodings. “Based on the flight patterns and the kind of usage of these 24-bit addresses, it does not seem like it is a mistake,” he told Reuters.
Two flights were particularly striking. On August 5–6, the drone initially transmitted the RAF Typhoon’s code, then switched signals three times over about 20 minutes before landing as the Rada Airlines plane. On November 18, the drone was airborne posing as the Belarusian Il-62 while the actual Rada aircraft simultaneously took off near Belarus headed for Tehran — meaning both planes were visible on trackers at the same time.
The Chinese military typically flies its drones dark, transmitting nothing at all. This deliberate broadcast of false identities is a different approach entirely.
Flight Paths Point Toward Taiwan, Not Routine Patrol
The 23 logged flights follow paths heading east from Hainan toward the Philippines, near the disputed Paracel Islands, and south along Vietnam’s coastline — covering waters frequented by submarines and approaching the Bashi Channel between Taiwan and the Philippines, a key choke point for China’s navy to access the Pacific. The aircraft flew star- and hourglass-shaped loitering patterns for hours at a time, a profile consistent with large military drone surveillance operations.
When analysts overlaid those 23 flight paths on a map of Taiwan, the routes concentrated around Taipei and extended along the island’s southern coastline. Analysts note this is suggestive, not confirmed PLA doctrine. But Neill described the image as “compelling: extensive rehearsals across the South China Sea to be deployed over Taiwan’s key points.” Eastern trajectories bring the aircraft close to Japanese and US bases in Okinawa and the Ryukyu island chain. He added that the operations look less like exercises and more like what US Indo-Pacific Command has described as rehearsals for a confrontation. Online flight tracker Amelia Smith first connected the YILO4200 call sign to the Wing Loong 2 by cross-referencing flight data with state press reports and government announcements.
Since mid-December, the same drone has also made several flights in northwest China, most recently on February 15, appearing as an anonymous Pilatus PC-12 turboprop. The deception program appears to extend well beyond the South China Sea.
What the Spoofing Actually Accomplishes
The tactic is unlikely to fool military-grade radars or experienced air traffic controllers looking closely. But that may not be the point. Neill put it plainly: “Anything the Chinese can do to sow confusion in the minds of their rivals is to their advantage. The US and its allies know that given the realities of highly automated conventional conflict, even milliseconds count along the kill chain of escalation.”
A false transponder signal on a busy flight tracker forces analysts and automated systems to pause and verify. In peacetime that is a minor nuisance. In the opening minutes of a conflict, that pause matters. The tactic could also mask sensitive surveillance activity or provide cover for monitoring submarine traffic through deep-water channels. It could equally be repurposed for misinformation during an active operation, flooding open-source channels with false aircraft identities while real assets move untracked.
China’s choice to impersonate a US-sanctioned Belarusian carrier tied to Wagner Group logistics, a British fighter jet, and a North Korean passenger plane is not random. Each identity introduces a different layer of confusion for any analyst trying to build a coherent air picture in real time.
Worth noting too: deliberately transmitting false ICAO 24-bit transponder addresses in international airspace may violate ICAO Annex 10 standards governing aviation communications. China has offered no explanation. Its defence ministry did not respond to Reuters’ questions about the flights or their purpose.
This Fits a Pattern DroneXL Has Been Tracking
The transponder spoofing operation does not exist in isolation. We have been watching China systematically expand its drone presence across the South China Sea for months. In February, we reported on China’s coastguard professionalizing drone operations at Scarborough Shoal, building training pipelines and standardizing long-endurance surveillance patrols over a disputed reef roughly 600 kilometers from its nearest major base. Earlier that month, we covered the Wing Loong X’s debut at the Singapore Airshow, where AVIC was pitching the platform’s maritime surveillance and anti-submarine capabilities to international buyers. The Wing Loong family is no longer experimental hardware — it is an operational system logging thousands of flight hours.
The drone build-up is part of a broader escalation. We also reported on how drone and missile deployments are tightening the Taiwan perimeter, and on the PLA demonstrating a 200-drone swarm controlled by a single soldier — a capability the Pentagon has described as a direct concern. In January, we covered China’s CH YH-1000S hybrid transport drone and its potential role in sustaining PLA forces in contested environments near Taiwan. And earlier still, we reported on Chinese drones breaching Vietnam’s airspace (in that case a Wing Loong-10) along some of the same corridors YILO4200 is now patrolling.
DroneXL’s Take
What makes this Reuters investigation genuinely alarming is not the technology. Transponder spoofing is not new. What’s alarming is the operational discipline behind it. Twenty-three logged flights. Star and hourglass patterns held for hours. Deliberate identity switches mid-flight. A fleet of fake personas chosen to maximize confusion across different monitoring systems and analysts.
This is not China testing whether the trick works. They know it works. This is China practicing the execution at scale, in real airspace, against real flight-tracking infrastructure, over routes that map directly onto Taiwan’s military geography.
The Wing Loong 2 is not a low-profile platform. It has a 20.5-meter wingspan and flies for hours in patterns that scream “military surveillance” to anyone watching. The spoofing does not hide the drone. It muddies the response to it. That is a more sophisticated goal, and it shows a military thinking carefully about the information environment, not just the physical one.
I’d expect two developments within the next six months. Flightradar24 and similar open-source platforms will build automated flagging for simultaneous duplicate transponder broadcasts — the same technical tell that exposed the November 18 flight, when the real Rada Il-62 and the spoofed drone appeared on trackers at the same time. That vulnerability is already public knowledge. China will need to adapt. And second, watch the open-source tracking community: the analyst who first identified YILO4200, Amelia Smith, did so by cross-referencing flight data with state media. That methodology will get refined fast now that this operation is documented.
Editorial Note: AI tools were used to assist with research and archive retrieval for this article. All reporting, analysis, and editorial perspectives are by Haye Kesteloo.
Discover more from DroneXL.co
Subscribe to get the latest posts sent to your email.
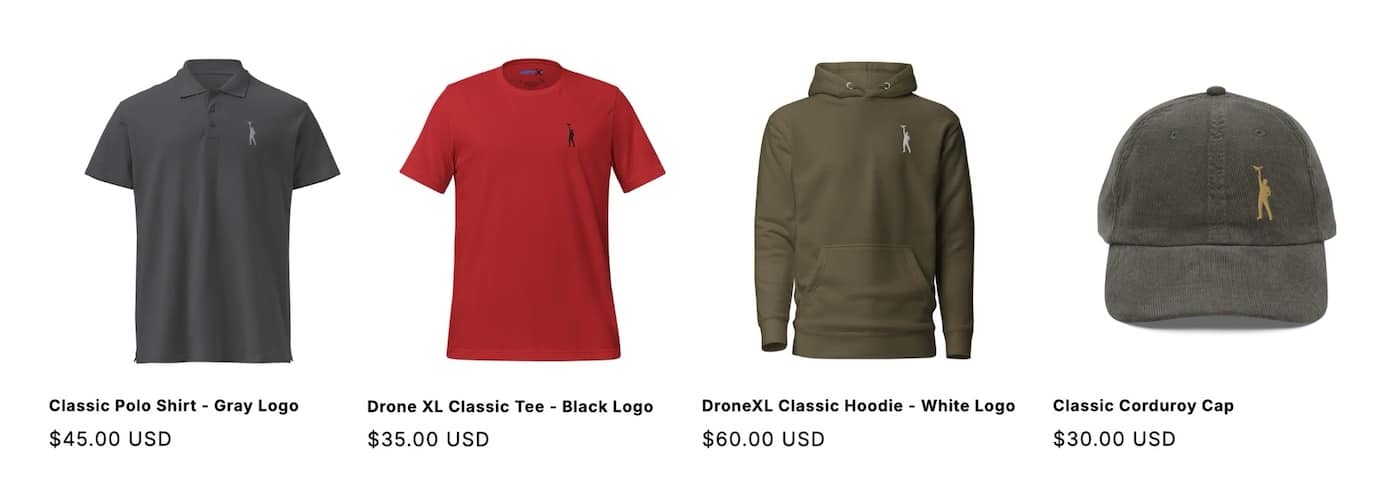
Check out our Classic Line of T-Shirts, Polos, Hoodies and more in our new store today!
MAKE YOUR VOICE HEARD
Proposed legislation threatens your ability to use drones for fun, work, and safety. The Drone Advocacy Alliance is fighting to ensure your voice is heard in these critical policy discussions.Join us and tell your elected officials to protect your right to fly.
Get your Part 107 Certificate
Pass the Part 107 test and take to the skies with the Pilot Institute. We have helped thousands of people become airplane and commercial drone pilots. Our courses are designed by industry experts to help you pass FAA tests and achieve your dreams.

Copyright © DroneXL.co 2026. All rights reserved. The content, images, and intellectual property on this website are protected by copyright law. Reproduction or distribution of any material without prior written permission from DroneXL.co is strictly prohibited. For permissions and inquiries, please contact us first. DroneXL.co is a proud partner of the Drone Advocacy Alliance. Be sure to check out DroneXL's sister site, EVXL.co, for all the latest news on electric vehicles.
FTC: DroneXL.co is an Amazon Associate and uses affiliate links that can generate income from qualifying purchases. We do not sell, share, rent out, or spam your email.














