Sammy Hacked 7,000 ROMO Vacuums. DJI Paid Him

Check out the Best Deals on Amazon for DJI Drones today!
A man tried to control his DJI robot vacuum with a PlayStation 5 controller. Accidentally discovered 7,000 other people’s robot vacuums wide open to the internet. Now DJI is paying him $30,000.
This story has everything. A PS5 controller. A floor map of a stranger’s house. And a $30,000 check from a company with a very specific history of paying $30,000 checks.
How You Accidentally Break Into 7,000 Homes
Sammy Azdoufal is a software engineer who owns a DJI Romo robot vacuum. He did not want to use a phone app to control it. Reasonable position. Phone apps are fine. A PlayStation 5 controller is better. Just like any other night playing Battlefield 6 after writing DroneXL articles.

Photo credit: Sammy Azdoufal LinkedIn
So he started reverse-engineering the authorization process between the Romo app and DJI’s cloud servers, which is the kind of sentence that sounds ominous but was really just a guy trying to avoid using a touchscreen to vacuum his living room.
What he found instead was a backend so wide open it would make a bank IT manager cry into their keyboard. The cloud server that controlled his Romo also controlled every other DJI Romo on the network. All 7,000 of them. Without needing a security PIN. Without needing much of anything, really.
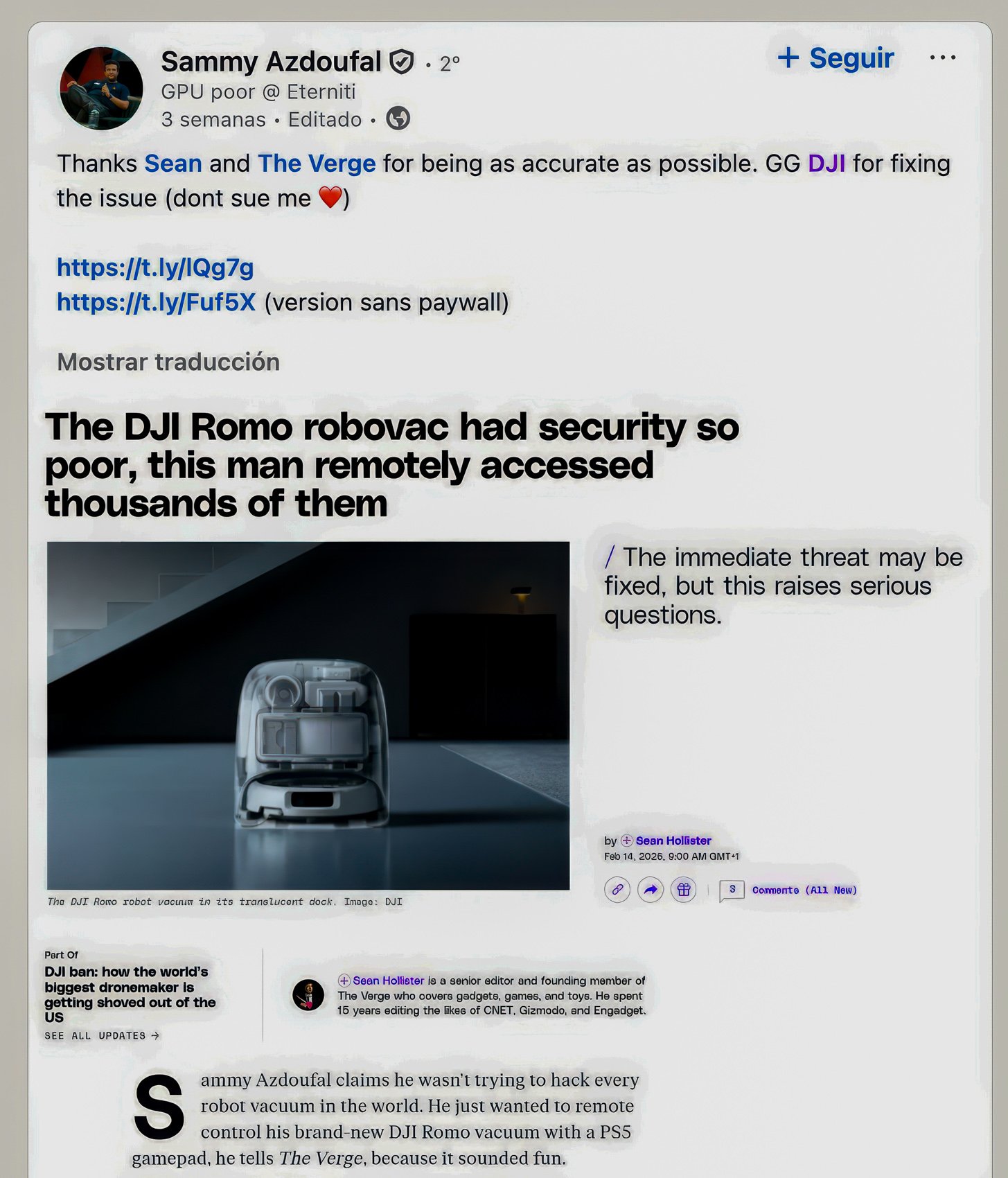
Azdoufal could access live video and audio feeds from thousands of homes. He could pull 2D floor plans of stranger’s houses. He could see IP addresses that roughly geolocated where those people lived.
He did not ask for any of this. He just wanted to vacuum his apartment with a game controller.
DJI confirmed it has paid $30,000 to an unnamed security researcher for a single discovery. Azdoufal shared the payment email with The Verge. DJI also confirmed it patched the PIN code vulnerability by late February and says a broader system upgrade covering the deeper architectural issues will be fully implemented within a month.
So far, so good. And now, a word from your friendly neighborhood DroneXL about that $30,000.
The Last Time DJI Offered Someone $30,000
The year was 2017. The person was Kevin Finisterre, a respected security researcher who found that DJI had accidentally published the private keys to all of its web domains and cloud storage accounts on GitHub. Passports. Government IDs.
Flight logs from what appeared to be military and government domains. All of it accessible because someone at DJI posted the keys to everything on a public code repository.
DJI confirmed the finding qualified for the top bounty of $30,000. Then the legal department got involved.
What followed was over 130 emails, an NDA that four separate lawyers independently described as “extremely risky” and “likely crafted in bad faith,” and a thinly veiled threat under the Computer Fraud and Abuse Act, a federal law that carries criminal penalties. When Finisterre decided he could not sign the agreement, DJI publicly called him a “hacker” and described his actions as unauthorized access.
Finisterre walked away from the $30,000. Then he published an 18-page PDF titled “Why I Walked Away From $30,000 of DJI Bounty Money” and made sure everyone knew exactly how that process had gone.
Multiple other researchers in the same program reportedly reached the same conclusion and also walked away. The bug bounty program was widely described in the security community as a PR move launched in a rush and executed in bad faith.
DJI eventually fired the developers responsible for the GitHub leak and sent breach notification letters to affected customers.The $30,000 remained in DJI’s account. Probably funded, at least in part, by every drone I have ever bought from them.
A $30,000 Check With Fine Print Written in 2017
So here is where things stand in 2026. DJI has paid Azdoufal. That is confirmed and real.
It is worth noting what that $30,000 actually represented in 2017. At the time DJI offered it to Finisterre, it was the largest bug bounty ever paid by any company to any security researcher. A record. Set deliberately. As a symbol.
A company serious about security research does not need to set a record bounty to prove it. It just builds a process that works quietly and consistently. The record-setting number was a headline, not a policy.
Then the legal department got involved, and the headline was all that remained.
The blog post DJI published about the Romo vulnerability claims the issues are fully resolved. Security researchers who reviewed the situation noted publicly that DJI declared the fix complete before the fix was actually complete.
The same pattern that played out in 2017, public claims of resolution ahead of actual resolution, showed up again here. Not identical circumstances. Close enough to notice.
DJI also still does not have a public-facing Chief Information Security Officer or any C-level security leadership. Security communications for a company with tens of millions of connected devices in the field are handled by the PR team.
The spokesperson who responded to The Verge about the Romo vulnerability is the same communications infrastructure that handles product launches and trade show announcements. That is a structural problem, not a personnel criticism. It means there is no accountable security executive whose job depends on getting these responses right.
The Romo also carries ETSI, EU, and UL security certifications, which is a detail worth sitting with for a moment. A device with three official security certifications had its entire 7,000-unit network accessible to anyone patient enough to reverse-engineer its app with a PS5 controller and a free afternoon. What those certifications are actually certifying is a reasonable question to ask out loud.
DroneXL’s Take
Here’s what I actually think: Sammy handled this exactly right, and DJI, at least this time, did too.
He found something serious. He reported it responsibly. He did not post it to Reddit for clout or sell it to a broker. He went to the company, showed them the problem, and waited. That is how this is supposed to work, and it does not always go that way.
The $30,000 is confirmed and real. The patches are rolling out. And unlike 2017, nobody ended up threatening anyone with federal computer fraud statutes. Progress is progress.
I will say this once and with full respect for Sammy’s judgment: he knows Kevin Finisterre personally, which means he already knows everything I was about to say. He went in with eyes open, read whatever needed reading, and made the call himself. That is not naivety. That is a guy who did his homework and decided the outcome was worth it.
Let’s be straight: the $30,000 almost certainly contains some portion of money that came directly from my own savings account, distributed across every DJI drone I have purchased over the years. I am choosing to view this as a charitable donation to internet security.
DJI builds incredible hardware. We have always said that. The question has always been what happens when someone finds a crack in the armor. This time, it went better. That deserves to be said.
Fly smart. Patch your robots.
Photo credit: Sammy Azdoufal LinkedIn , DJI, Kevin Finisterre.
Discover more from DroneXL.co
Subscribe to get the latest posts sent to your email.
Check out our Classic Line of T-Shirts, Polos, Hoodies and more in our new store today!
MAKE YOUR VOICE HEARD
Proposed legislation threatens your ability to use drones for fun, work, and safety. The Drone Advocacy Alliance is fighting to ensure your voice is heard in these critical policy discussions.Join us and tell your elected officials to protect your right to fly.
Get your Part 107 Certificate
Pass the Part 107 test and take to the skies with the Pilot Institute. We have helped thousands of people become airplane and commercial drone pilots. Our courses are designed by industry experts to help you pass FAA tests and achieve your dreams.

Copyright © DroneXL.co 2026. All rights reserved. The content, images, and intellectual property on this website are protected by copyright law. Reproduction or distribution of any material without prior written permission from DroneXL.co is strictly prohibited. For permissions and inquiries, please contact us first. DroneXL.co is a proud partner of the Drone Advocacy Alliance. Be sure to check out DroneXL's sister site, EVXL.co, for all the latest news on electric vehicles.
FTC: DroneXL.co is an Amazon Associate and uses affiliate links that can generate income from qualifying purchases. We do not sell, share, rent out, or spam your email.