DJI Pilot app shares same security flaws as DJI Go 4, says Synacktiv

Check out the Best Deals on Amazon for DJI Drones today!
About ten days ago, this story was published in the NY Times highlighting the security flaws found in the DJI Go 4 app for the Android platform by security researchers from the French company Synacktiv. Today, the company releases a new statement claiming that the DJI Pilot app for commercial and enterprise customers has the same security concerns
DJI Pilot app shares same security flaws as DJI Go 4, according to Synacktiv
Synacktiv, a French security research company that has also worked for DJI’s competitors, released a statement claiming that the DJI Pilot app for commercial and enterprise customers shares many of the same security flaws as the DJI Go 4 app. The issues are related to the apps running on Google’s Android platform, not Apple’s iOS.
Synacktiv’s initial report on the DJI Go 4 app was picked up by the NY Times and July 23, 2020. In a statement, the company says that
“We found similar issues to those listed in our previous blogpost in the application, such as a forced update mechanism.”
The DJI Pilot app is used to control the DJI Matrice, DJI Phantom 4, DJI Mavic Pro, and DJI Mavic 2 Enterprise drones.
Synacktiv’s key findings on the DJI Pilot app
Here are the key findings from Synacktiv:
- The professional DJI Pilot application is protected using the same packer as the consumer-grade DJI Go 4 application
- The professional DJI Pilot application includes the same forced upgrade mechanism as the one present in its consumer-grade applications
- The “offline” Local Data Mode requires an Internet connection in order to install unlocking certificates
Synacktiv points out that the forced upgrade mechanism is,
“very similar to command and control servers encountered with malwares. Given the wide permissions required by DJI Pilot (access contacts, microphone, camera, location, storage, change network connectivity, etc.), the DJI servers have almost full control over the user’s phone.”
DJI’s Local Data Mode does allow the drone to be disconnected from the internet while being operated, however, Synactiv points out that in order to unlock flying over certain sensitive areas, the user has to deactivate the Local Date Mode temporarily and thus allowing network communications for a limited time. The research firm also points out that the unlock certificate is linked to a specific aircraft and user account and thus may “allow specific targeting of sensitive users.”
DroneXL’s take
We have reached out to DJI for a response on this latest report from Synacktiv and will let you know once we receive that. Furthermore, we do wonder who is behind this research? Are these research projects done by Synacktiv or does another party pay for Synacktiv to look into these DJI apps? We will ask them.
Can you, @Synacktiv, confirm or deny that @parrot is behind your reports on security flaws in the DJI Pilot and DJI Go 4 app? I think we deserve to know. @djiglobal @DJIEnterprise #datasecurity #drone #drones #uas #uav https://t.co/rUy0rR6IPN
— DroneXL (@DroneXL1) August 4, 2020
Stay in touch!
If you’d like to stay up to date with all the latest drone news, scoops, rumors, and reviews, then follow us on Twitter, Facebook, YouTube, Instagram or…
Subscribe to our Daily Drone News email.*
Submit tips If you have information or tips that you would like to share with us, feel free to submit them here. Support DroneXL.co: You can support DroneXL.co by using these links when you make your next drone purchase: Adorama, Amazon, B&H, BestBuy, eBay, DJI, Parrot, and Yuneec. We make a small commission when you do so at no additional expense to you. Thank you for helping DroneXL grow! FTC: DroneXL.co uses affiliate links that generate income.
* We do not sell, share, rent out or spam your email, ever. Our email goes out on weekdays around 5:30 p.m.
Discover more from DroneXL.co
Subscribe to get the latest posts sent to your email.
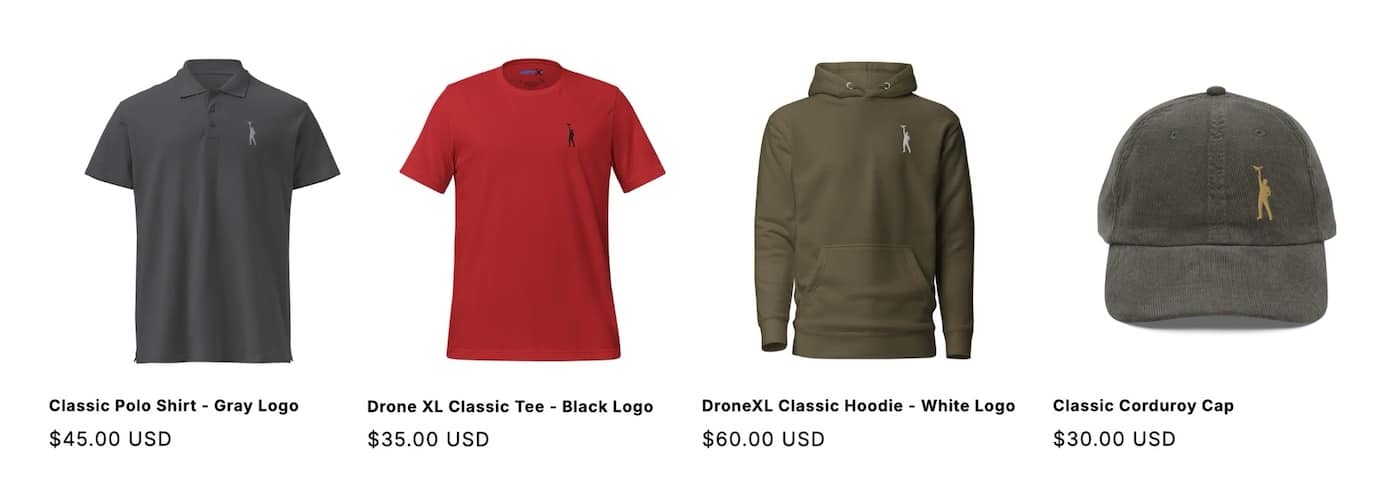
Check out our Classic Line of T-Shirts, Polos, Hoodies and more in our new store today!
MAKE YOUR VOICE HEARD
Proposed legislation threatens your ability to use drones for fun, work, and safety. The Drone Advocacy Alliance is fighting to ensure your voice is heard in these critical policy discussions.Join us and tell your elected officials to protect your right to fly.
Get your Part 107 Certificate
Pass the Part 107 test and take to the skies with the Pilot Institute. We have helped thousands of people become airplane and commercial drone pilots. Our courses are designed by industry experts to help you pass FAA tests and achieve your dreams.

Copyright © DroneXL.co 2026. All rights reserved. The content, images, and intellectual property on this website are protected by copyright law. Reproduction or distribution of any material without prior written permission from DroneXL.co is strictly prohibited. For permissions and inquiries, please contact us first. DroneXL.co is a proud partner of the Drone Advocacy Alliance. Be sure to check out DroneXL's sister site, EVXL.co, for all the latest news on electric vehicles.
FTC: DroneXL.co is an Amazon Associate and uses affiliate links that can generate income from qualifying purchases. We do not sell, share, rent out, or spam your email.




















