DJI’s response to the security weakness reported in the NY Times

Check out the Best Deals on Amazon for DJI Drones today!
DJI released the following statement (see below) in response to the security weakness found in DJI drones mentioned in this article from the NY Times. We reached out to DJI to get some clarification on a specific part of their response.
DJI’s response to the security weakness reported in the NY Times
When reading the official response from DJI, the one thing that stood out to me was the following phrase:
“…have found no evidence of unexpected data transmission connections from DJI’s apps designed for government and professional customers.”
This sentence seems to leave open the possibility that unexpected data transmission connections might have taken place for consumer drones. We reached out to DJI to get some clarification on that and here’s what they said:
We phrased that line because it refers primarily to the Booz Allen Hamilton study (which covered Government Edition M600 Pro, Government Edition Mavic Pro, and regular old Mavic 2 Enterprise) and the DHS study for DOI (which, again, covered Government Edition M600 Pro and Government Edition Mavic Pro). We did not want to imply they had evaluated more systems than they really did.
HOWEVER, no one has ever shown unexpected data transmission from our consumer products either. The Kivu report is now more than 2-1/2 years old, but it covered the Spark, the original Mavic Pro, the Phantom 4 Pro and the Inspire 2, running GO 4 on both Android and iOS.
DJI doesn’t flat-out deny the possibility of any consumer data having ever been transferred to China, but it does say that it has never been proven. I guess we will have to make up our own mind in this case. It is important to point out that you can prevent any data from being shared with DJI by simply turning off the WiFi on your phone or using Local Data Mode in the DJI Pilot app.
Now, it comes as no surprise that DJI is catching most, if not all, of the flack since it is by far the largest drone manufacturer, and it is a Chinese company. However, I wonder if companies like Parrot or Autel Robotics would invite and withstand the scrutiny that DJI has had to endure when it comes to data security concerns.
Here’s DJI’s official response:
DJI Statement On Recent Reports From Security Researchers
DJI takes the security of its apps and the privacy of customer data seriously. While these researchers discovered two hypothetical vulnerabilities in one of our recreational apps, nothing in their work is relevant to, or contradicts, the reports from the U.S. Department of Homeland Security, Booz Allen Hamilton and others that have found no evidence of unexpected data transmission connections from DJI’s apps designed for government and professional customers.
These researchers found typical software concerns, with no evidence they have ever been exploited. The app update function described in these reports serves the very important safety goal of mitigating the use of hacked apps that seek to override our geofencing or altitude limitation features. As the only major drone manufacturer with a Bug Bounty Program, we encourage all researchers to responsibly disclose security concerns about our products at security.dji.com.
We design our systems so DJI customers have full control over how or whether to share their photos, videos and flight logs, and we support the creation of industry standards for drone data security that will provide protection and confidence for all drone users.
We hope these details provide more context to understand these reports:
- When our systems detect that a DJI app is not the official version – for example, if it has been modified to remove critical flight safety features like geofencing or altitude restrictions – we notify the user and require them to download the most recent official version of the app from our website. In future versions, users will also be able to download the official version from Google Play if it is available in their country. If users do not consent to doing so, their unauthorized (hacked) version of the app will be disabled for safety reasons.
- Unauthorized modifications to DJI control apps have raised concerns in the past, and this technique is designed to help ensure that our comprehensive airspace safety measures are applied consistently.
- Because our recreational customers often want to share their photos and videos with friends and family on social media, DJI integrates our consumer apps with the leading social media sites via their native SDKs. We must direct questions about the security of these SDKs to their respective social media services. However, please note that the SDK is only used when our users proactively turn it on.
- DJI GO 4 is not able to restart itself without input from the user, and we are investigating why these researchers claim it did so. We have not been able to replicate this behavior in our tests so far.
- The hypothetical vulnerabilities outlined in these reports are best characterized as potential bugs, which we have proactively tried to identify through our Bug Bounty Program, where security researchers responsibly disclose security issues they discover in exchange for payments of up to $30,000. Since all DJI flight control apps are designed to work in any country, we have been able to improve our software thanks to contributions from researchers all over the world, as seen on this list.
- The MobTech and Bugly components identified in these reports were previously removed from DJI flight control apps after earlier researchers identified potential security flaws in them. Again, there is no evidence they were ever exploited, and they were not used in DJI’s flight control systems for government and professional customers.
- The DJI GO4 app is primarily used to control our recreational drone products. DJI’s drone products designed for government agencies do not transmit data to DJI and are compatible only with a non-commercially available version of the DJI Pilot app. The software for these drones is only updated via an offline process, meaning this report is irrelevant to drones intended for sensitive government use. A recent security report from Booz Allen Hamilton audited these systems and found no evidence that the data or information collected by these drones is being transmitted to DJI, China, or any other unexpected party.
- This is only the latest independent validation of the security of DJI products following reviews by the U.S. National Oceanic and Atmospheric Administration, U.S. cybersecurity firm Kivu Consulting, the U.S. Department of Interior and the U.S. Department of Homeland Security.
- DJI has long called for the creation of industry standards for drone data security, a process which we hope will continue to provide appropriate protections for drone users with security concerns. If this type of feature, intended to assure safety, is a concern, it should be addressed in objective standards that can be specified by customers. DJI is committed to protecting drone user data, which is why we design our systems so drone users have control of whether they share any data with us. We also are committed to safety, trying to contribute technology solutions to keep the airspace safe.
Stay in touch!
If you’d like to stay up to date with all the latest drone news, scoops, rumors, and reviews, then follow us on Twitter, Facebook, YouTube, Instagram or…
Subscribe to our Daily Drone News email.*
Submit tips If you have information or tips that you would like to share with us, feel free to submit them here. Support DroneXL.co: You can support DroneXL.co by using these links when you make your next drone purchase: Adorama, Amazon, B&H, BestBuy, eBay, DJI, Parrot, and Yuneec. We make a small commission when you do so at no additional expense to you. Thank you for helping DroneXL grow! FTC: DroneXL.co uses affiliate links that generate income.
* We do not sell, share, rent out or spam your email, ever. Our email goes out on weekdays around 5:30 p.m.
Discover more from DroneXL.co
Subscribe to get the latest posts sent to your email.
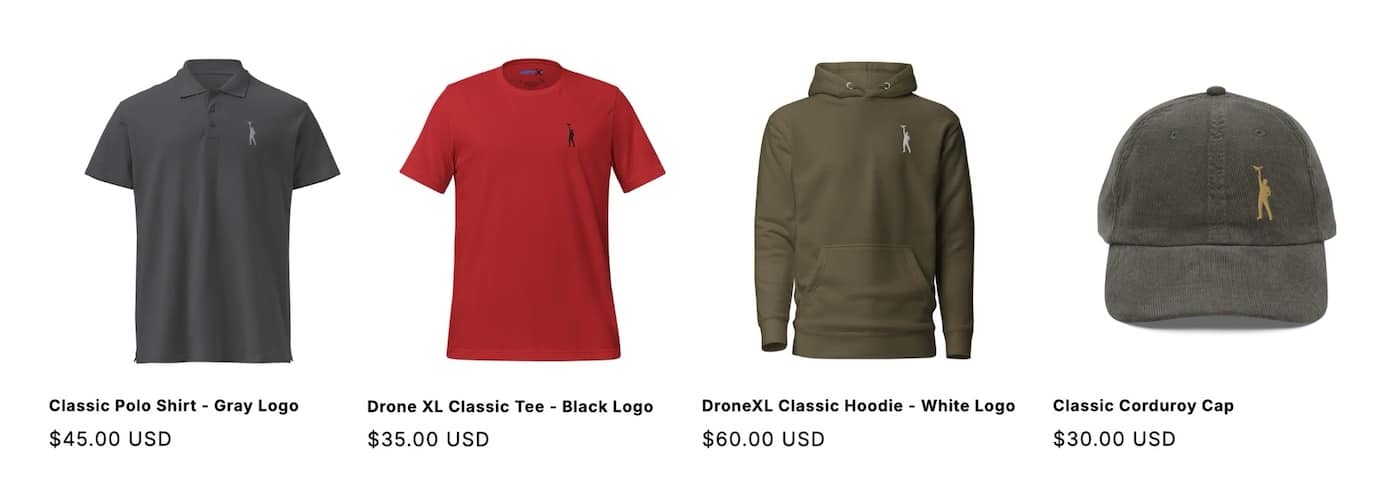
Check out our Classic Line of T-Shirts, Polos, Hoodies and more in our new store today!
MAKE YOUR VOICE HEARD
Proposed legislation threatens your ability to use drones for fun, work, and safety. The Drone Advocacy Alliance is fighting to ensure your voice is heard in these critical policy discussions.Join us and tell your elected officials to protect your right to fly.
Get your Part 107 Certificate
Pass the Part 107 test and take to the skies with the Pilot Institute. We have helped thousands of people become airplane and commercial drone pilots. Our courses are designed by industry experts to help you pass FAA tests and achieve your dreams.

Copyright © DroneXL.co 2026. All rights reserved. The content, images, and intellectual property on this website are protected by copyright law. Reproduction or distribution of any material without prior written permission from DroneXL.co is strictly prohibited. For permissions and inquiries, please contact us first. DroneXL.co is a proud partner of the Drone Advocacy Alliance. Be sure to check out DroneXL's sister site, EVXL.co, for all the latest news on electric vehicles.
FTC: DroneXL.co is an Amazon Associate and uses affiliate links that can generate income from qualifying purchases. We do not sell, share, rent out, or spam your email.




















