Booz Allen Hamilton finds no unauthorized data transfer from DJI drones

Check out the Best Deals on Amazon for DJI Drones today!
A study from Booz Allen Hamilton in partnership with PrecisionHawk concludes there has not been any unauthorized data transfer from DJI drones, that were previously used by the US government, to the Chinese drone maker or government. You can download the executive summary of the report here.
No unauthorized data transfer from DJI drones back to China
News outlet The Hill reports that this study is the latest call into question allegations from several lawmakers who have pushed for federal agencies to stop using Chinese made drones over concerns that they might share data with the Chinese Communist Party (CCP).
In an interview, Brandon Schulman, DJI’s vice president of policy and legal affairs said:
That’s the allegation that we’ve seen the past two years or more repeated by policymakers and in some cases our competitors as a reason to enact policy that would take away the ability to choose which products to use in a mission. None of those have been accompanied by evidence or analysis demonstrating that there’s a factual basis behind the allegation.
In 2019, PrecisionHawk established its Unmanned Aerial Intelligence Technology Center of Excellence (UAS COE), which is backed by the cybersecurity expertise of leading government technology firm Booz Allen Hamilton.
Booz Allen Hamilton said that it has not found any evidence of unauthorized data transmissions in its analysis of three DJI drone models that at one point were used by the US government. The three specific DJI commercial drones that were examined in this report are the Government Edition DJI Mavic Pro, the Government Edition DJI Matrice 600 Pro, and the DJI Mavic 2. Enterprise.
PrecisionHawk stated that: the Booz Allen testing covered DJI’s Government Edition Mavic Pro and Matrice 600 Pro drones, as well as the Mavic 2 Enterprise. This security-focused testing did not identify data connections made by the drone platforms to DJI or Chinese servers. The testing did identify potential vulnerabilities associated with one or more of the three drone platforms that could be exploited or triggered by a threat source. Nearly all of those vulnerabilities require physical access to the drone itself, or for the attacker to be within direct radio range during specific operations. When drones are operated and managed by trusted and trained personnel, allowing for a trusted chain of control to be incorporated into standard operating procedures (SOPs), vulnerabilities requiring physical access can be significantly minimized.
DJI is the largest manufacturer of drones in the world and has long stated that no data is transferred from its drones to either the Chinese government or to the drone company itself. Drone operators have the option to store aerial images and videos from their drones on DJI’s servers but they do not have to do so. See Brendan Schulman’s interview for more background on this.
DJI responded by saying that:
Today, the UAS COE released an executive summary of the audit, which we encourage all customers to read fully. It is another independent validation of the security of DJI products following reviews by the U.S. National Oceanic and Atmospheric Administration, U.S. cybersecurity firm Kivu Consulting, U.S. Department of Interior, U.S. Department of Homeland Security, and others. The audit is a critical step toward ensuring emerging drone technology is secure and able to be trusted for government and enterprise operations.
The audit found no evidence of data transmission connections between these drones and DJI, China, or any other unexpected party. From our perspective, this important finding from an independent, globally recognized leader in cybersecurity indicates that DJI customers have control over the data they collect when using our drones, contradicting reports that data from DJI devices is surreptitiously routed to other parties.
Back in 2017, the US Army stopped using DJI drones. And the Interior Department of the United States grounded its entire drone fleet temporarily in October last year. The United States Department of the Interior started with a temporary grounding of all of its drones that were manufactured in China or contained Chinese made parts in October of last year. Early on in 2020, Interior Secretary David Bernhardt took things one step further and continued the temporary grounding of all of the agency’s drones.
In September, a bipartisan group of senators introduced legislation, that would stop all federal agencies from using drones that have been manufactured or assembled in China. More recently, Senator Martha McSally (Rep-AZ) proposed a bill that would prohibit any federal funding from being used to purchase drones manufactured in China. Neither of these two bills has moved out of committee according to The Hill.
The proposed bills and other actions from government bodies result from concerns of a new Chinese law that was introduced in 2017, that requires Chinese companies to transfer any data when requested for state intelligence work. Other companies that have seen increased pressure are Chinese telecommunication companies such as Huawei, ZTE, and the social media app TikTok.
Even though the allegations of unauthorized information sharing have been unsubstantiated, they are part of a larger push to eliminate the use of any Chinese made equipment by the US federal government.
Stay in touch!
If you’d like to stay up to date with all the latest drone news, scoops, rumors, and reviews, then follow us on Twitter, Facebook, YouTube, Instagram or…
Subscribe to our Daily Drone News email.*
Submit tips If you have information or tips that you would like to share with us, feel free to submit them here. Support DroneXL.co: You can support DroneXL.co by using these links when you make your next drone purchase: Adorama, Amazon, B&H, BestBuy, eBay, DJI, Parrot, and Yuneec. We make a small commission when you do so at no additional expense to you. Thank you for helping DroneXL grow! FTC: DroneXL.co uses affiliate links that generate income.
* We do not sell, share, rent out or spam your email, ever. Our email goes out on weekdays around 5:30 p.m.
Photo: DJI
Discover more from DroneXL.co
Subscribe to get the latest posts sent to your email.
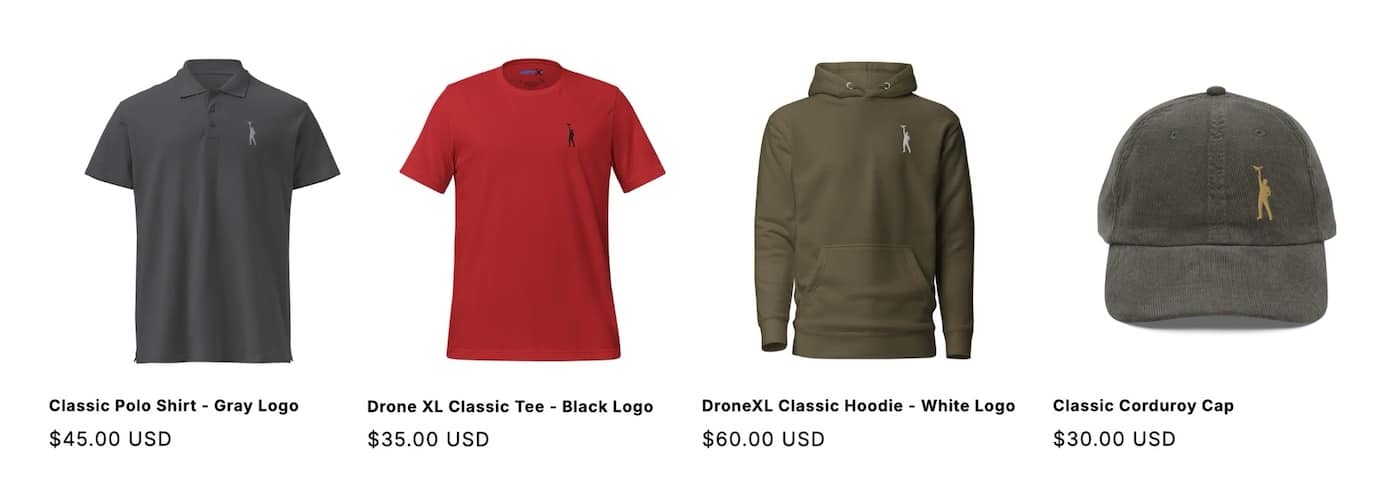
Check out our Classic Line of T-Shirts, Polos, Hoodies and more in our new store today!
MAKE YOUR VOICE HEARD
Proposed legislation threatens your ability to use drones for fun, work, and safety. The Drone Advocacy Alliance is fighting to ensure your voice is heard in these critical policy discussions.Join us and tell your elected officials to protect your right to fly.
Get your Part 107 Certificate
Pass the Part 107 test and take to the skies with the Pilot Institute. We have helped thousands of people become airplane and commercial drone pilots. Our courses are designed by industry experts to help you pass FAA tests and achieve your dreams.

Copyright © DroneXL.co 2026. All rights reserved. The content, images, and intellectual property on this website are protected by copyright law. Reproduction or distribution of any material without prior written permission from DroneXL.co is strictly prohibited. For permissions and inquiries, please contact us first. DroneXL.co is a proud partner of the Drone Advocacy Alliance. Be sure to check out DroneXL's sister site, EVXL.co, for all the latest news on electric vehicles.
FTC: DroneXL.co is an Amazon Associate and uses affiliate links that can generate income from qualifying purchases. We do not sell, share, rent out, or spam your email.


















