DJI drone operator’s location can easily be intercepted

Check out the Best Deals on Amazon for DJI Drones today!
Hackers, or security researchers, have figured out how to decode the radio signals that every DJI drone sends out. This lets them know exactly where the DJI drone operator is.
UPDATE: DJI RESPONDS TO CONCERNS ABOUT DRONE PILOTS’ LOCATIONS BEING PUBLIC
At the Network and Distributed System Security Symposium (NDSS) in San Diego last week, security researchers from Ruhr University Bochum and the CISPA Helmholtz Center for Information Security showed how they could decode the radio signals of DJI drones.
By reverse engineering the drone’s radio protocol, called DroneID, they discovered that every DJI drone’s DroneID communications broadcast not only its own GPS location and a unique identifier but also the GPS coordinates of its operator.
This means that anyone with cheap radio hardware and access to a new software tool can intercept and decode the drone’s broadcasts to pinpoint the operator’s location, potentially posing serious security and privacy concerns.
The DroneID system (better known as DJI Aeroscope) was developed to give governments, regulators, and law enforcement agencies the ability to track drones and stop the inappropriate use of them.

But, hackers and security researchers have been warning for a year that DroneID is not encrypted, contrary to what DJI originally stated, and is accessible to anyone who can intercept its radio transmissions. This vulnerability exists because DroneID does not use a public key infrastructure.
Along with a researcher from the University of Tulsa, researchers from Ruhr University Bochum and the CISPA Helmholtz Institute for Information Security have proven how the signal can be fully decoded and read.
This enables any hacker to monitor the drone’s operator, even if they are miles away, WIRED reports.
The German research group has made their preliminary results on how to collect and decode DroneID data publicly available through the deployment of a prototype tool.
Their findings have published in a report, titled: “Drone Security and the Mysterious Case of DJI’s DroneID.”
In the reports, the researcher conclude that: “We show that the transmitted data is not encrypted, but accessible to anyone, compromising the drone operator’s privacy. Second, we conduct a comprehensive analysis of drone security: Using a combination of reverse engineering, a novel fuzzing approach tailored to DJI’s communication protocol, and hardware analysis, we uncover several critical flaws in drone firmware that allow attackers to gain elevated privileges on two different DJI drones and their remote control.”
Having such complete access to the system makes it possible to disable or get around countermeasures and abuse drones.
“In total, we found 16 vulnerabilities, ranging from denial of service to arbitrary code execution. 14 of these bugs can be triggered remotely via the operator’s smartphone, allowing us to crash the drone mid-flight,” the researchers explain.
In April last year, DJI confessed to The Verge that the broadcasts were, in fact, not encrypted after it was demonstrated by security researcher Kevin Finisterre that certain DroneID data could be intercepted using a commercially available Ettus software-defined radio.
Popular DJI drone models already broadcast operator’s location
German researchers have now taken the investigation into DJI’s initial encryption claim one step further by reverse engineering DroneID by studying the firmware of a DJI drone as well as the radio communications between the drone and its controller.
The researchers were able to demonstrate their findings using a DJI Mini 2, a DJI Air 2, a DJI Mavic 2 Pro and Zoom, and even the latest flagship drone, the DJI Mavic 3.

They made a device that can pick up DroneID transmissions with either an Ettus software-defined radio or a much cheaper HackRF radio.
With this set-up and their software, it is possible to correctly decode the signal and find out where the drone operator is, just like DJI’s Aeroscope does.
This new data draws attention to the substantial concerns regarding privacy and operational security that are raised by DroneID, in particular for operators of DJI drones that are used in conflict zones.
Due to the fact that the DroneID broadcasts an operator’s location, it is possible for it to draw the attention of hostile forces, putting the operator’s safety in jeopardy.
This information is particularly important for individuals operating DJI drones in the ongoing conflict between Ukraine and Russia.
DJI has yet to respond on the DroneID concerns
WIRED reached out to DJI for clarification on the DroneID issue and the fact that unencrypted location data of DJI drone operators is being broadcast, but the dronemaker has yet to respond.
However, Brendan Schulman, who served as DJI’s former Vice President of Policy and Legal Affairs, asserted that DroneID was intended to operate in the manner in which it currently does.
Schulman says that DJI made DroneID because the U.S. government wanted a system for keeping track of drones.
Under this system, drone manufacturers would send out the location of the operator and a unique identifier for the drone. This information would be easy for anyone to find.
“FAA’s mandatory Remote ID will not only be unencrypted, but by design accessible to everyone nearby with a smartphone. AeroScope was from its start in 2017, a proof-of-concept for FAA/EASA drone Remote ID,” Schulman explained last year.
The Federal Aviation Administration (FAA) and other government organizations were interested in putting the system into place because it would improve public safety.
Schulman also said that the problem is not unique to DJI and that when the FAA Remote ID requirements become mandatory later this year, it is likely that all consumer drones will have a system similar to the one described above.
Schulman’s answer didn’t say anything about the fact that most DJI drone owners probably don’t know that their drones already send out information about where the operator is located.
According to Bender of the University of Tulsa, this lack of openness from DJI has led to confusion among users.
Not only DJI’s own Aeroscope devices are capable of intercepting the unencrypted location data that is provided by DJI’s drones; anyone with a low-cost receiver and the appropriate software may do it as well.
This will likely have significant repercussions for the ways in which drones are utilized in conflict zones and other hostile environments.
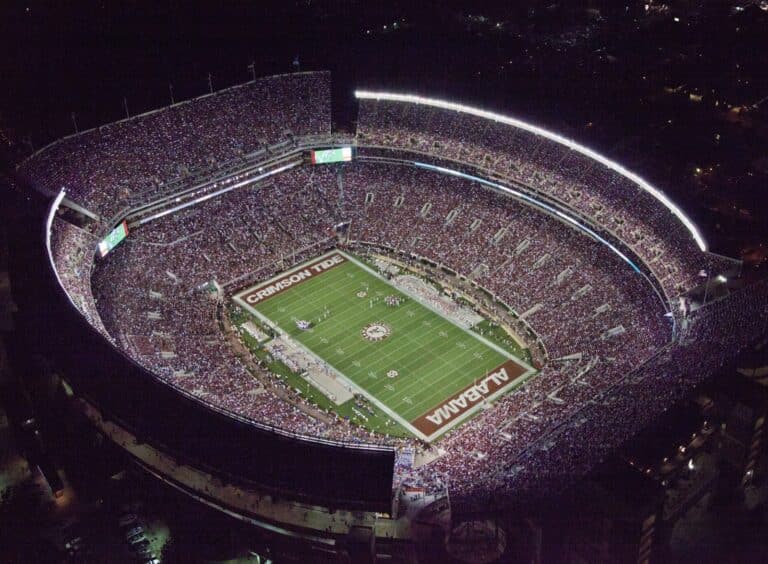
Photos courtesy of Ruhr University Bochum and CISPA Helmholtz Center for Information Security
Discover more from DroneXL.co
Subscribe to get the latest posts sent to your email.
Check out our Classic Line of T-Shirts, Polos, Hoodies and more in our new store today!
MAKE YOUR VOICE HEARD
Proposed legislation threatens your ability to use drones for fun, work, and safety. The Drone Advocacy Alliance is fighting to ensure your voice is heard in these critical policy discussions.Join us and tell your elected officials to protect your right to fly.
Get your Part 107 Certificate
Pass the Part 107 test and take to the skies with the Pilot Institute. We have helped thousands of people become airplane and commercial drone pilots. Our courses are designed by industry experts to help you pass FAA tests and achieve your dreams.

Copyright © DroneXL.co 2026. All rights reserved. The content, images, and intellectual property on this website are protected by copyright law. Reproduction or distribution of any material without prior written permission from DroneXL.co is strictly prohibited. For permissions and inquiries, please contact us first. DroneXL.co is a proud partner of the Drone Advocacy Alliance. Be sure to check out DroneXL's sister site, EVXL.co, for all the latest news on electric vehicles.
FTC: DroneXL.co is an Amazon Associate and uses affiliate links that can generate income from qualifying purchases. We do not sell, share, rent out, or spam your email.


















Why is this even a concern?? With the government mandating Remote ID you can get this information from an app on your phone. No special equipment or software needed.
Jay,
It’s a huge concern for private citizens who fly UAV’s for so many reasons. Did you even read up on the privacy concerns or take note of drones usage in “conflict zones?”
Bottom line is this….Take this as a very dumbed down version of an example for you to understand. It’s the same principle and issue.
The general public does not have access to look your up or any information about you by running your license plate from your car. Say you cut someone off or worse someone wanted to find out where you lived because you drove a nice ride. Or they thought your wife or daughter was attractive. (several examples to start with) Would you want some stranger or violent thug, robber, rapist, to be able to look you up and come to your house later on? All because they were able to run your plates from an app? NO, you would not!
There’s good reason why this data base is off limits to the general public.
The same goes for drones and their pilots. I have thousands of dollars worth of drone equipment. I also fly them with my family. I don’t want paranoid uneducated people, crooks, knowing my identity or location for safety alone. Let alone, I don’t want people knowing the equipment I have.
I’m perfectly fine with law enforcement and the FAA to know who I am and where I am at. Because I don’t fly illegally. Plus it’s just how it is. We have to have some sort of governing systems in place to keep order and enforce safety. Right?
The issue is, with any random Jo blow knowing where am at and what equipment I own. That’s where privacy and safety is a huge concern. The general public should never have access to my location or information.
It’s no different than someone being able to pull your plate number. Police can’t even pull your license plate without reasonable cause. I know these things because I worked for law enforcement for several years.
That’s what the problem is. If you were a UAV operator, you’d know this. Better yet an educated UAV operator. Either way this information should never be allowed to be viewed by the general public for many reasons. I listed on a couple of scenarios as to why.
This must be why the DoD has banned them and other state agencies. Soon you won’t be able to buy DJI in America.
What I don’t understand is if you’re under the weight requirement 250 g (like the mini Pro 3 249g) and you don’t have to register with the FAA because of this. Why are you subject to remote ID and other rules? When by definition you are an exception..
As of September 16th, 2023: When you fly a drone that weighs less than 250 grams for recreational purposes, you do not need to register with the FAA, and in that case you are exempt from Remote ID. However, if you fly a drone that weighs less than 250 grams commercially (Part 107), you will need to register with the FAA and thus you will be subject to Remote ID. Hope this helps.